In this article
Share
A Balanced security approach is a fundamental best practice when it comes to securing your payment infrastructure. Encryption and tokenization, firewalls for back-office systems or mobile device management (MDM) solutions can play a major role in preventing data theft — but a purely technology-based strategy isn’t a cure-all. Employees, from high-level executives to in-store associates, are an essential piece of your tiered security strategy.
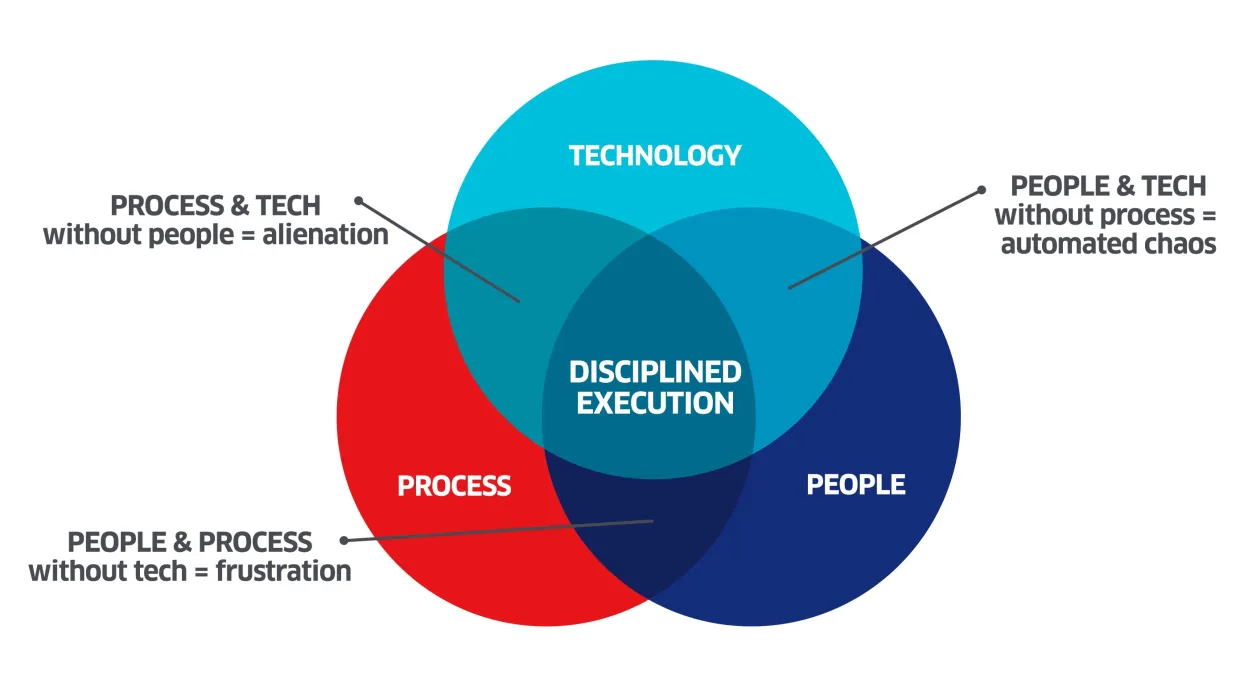
A balanced security approach pulls together and maintains three main elements: technology, process and people. A fine balance between the three is required to get to a state of disciplined execution of your security plan. If any of the elements are missing or not taken seriously, the plan doesn’t work. Consider it this way:
Technology is the baseline defense against potential threats. Attempting to execute security without technology leaves employees with a frustrating lack of tools for the job effectively. Clear guidelines and procedures help employees know what to do with the technology under all circumstances. Without process it’s just automated chaos, and defense technology needs to be implemented and used properly according to process; it can’t be left in a closet to function on its own. Alienating people from the security plan leaves major holes that would-be data thieves can take advantage of.
People are a crucial piece of this balancing act. In the manufacturing world, production lines have a "STOP" button. Every employee working on that line is empowered and applauded for recognizing problems and halting the line before things get out of hand. Information security needs to work the same way. It starts at the grassroots where your people need to recognize that they are an integral part of the team protecting your infrastructure — they are your first line of defense against attacks like social engineering. But they don’t come immediately equipped with the tools to recognize threats and fraud. Social Engineering and human error combine to be the leading first actions in most data breaches — however, this is a risk that can easily be avoided with regular training that is tailored to your employees’ roles.
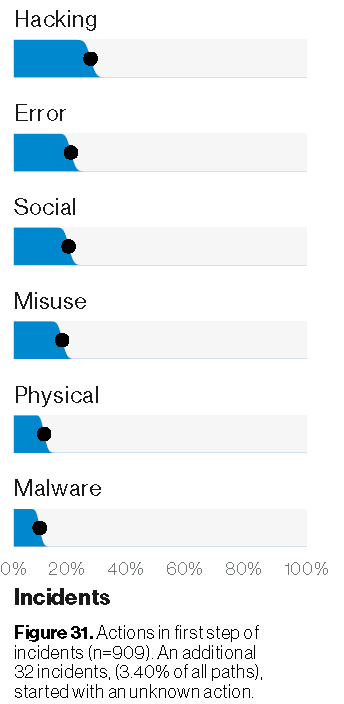
Source: 2019 Verizon Data Breach Incident Report. Figure shows actions in the first step of incidents.
Equipping your human defense
First and foremost, hire competent, trustworthy and qualified employees. It’s easier to teach new technology, procedures and processes to someone with a strong foundation. As a starting point for grassroots security, equip your in-store associates with these six essential best practices:
- Regularly inspect payment acceptance devices for any signs of tampering which allow cybercriminals to easily capture sensitive data including credit card information.
- Keep an eye out for suspicious behavior as cybercriminals often pose as customers or technicians to gain access to your payment solutions.
- Be aware of protocols to follow if someone does pose as a technician, such as calling your solution provider or manufacturer to confirm any scheduled visits.
- Understand what a safe and secure payment transaction looks like as opposed to a potentially fraudulent one.
- Use unique passwords for every account and don’t share them with other employees. Also use multi-factor authentication where possible.
- Practice your incident procedure to ensure that everyone knows what to do in the event that you find something suspicious or something does go wrong.
While technology is constantly evolving to better secure our data, cybercriminals are keeping pace. Your security solution should be bolstered by a balanced adoption of technology, process and people. Making sure your employees are aware of new threats in the market and are prepared to defend against unexpected fraud is an essential part of any rounded security plan. Want to know more about how to protect your payment infrastructure from all angles? Drop us a line!
Steven Bowles is the Regional Security Officer & Director of Security Solutions at Ingenico Group, North America